Mac Os X 10.8 4 Dmg Torrent Click on the below-given link to download the complete offline Mac OS X Mountain Lion 10.8.3 DMG image for x86 and x64 architecture. It is a very secure and stable OS for your Apple Computer. The 10.8.4 update is recommended for all OS X Mountain Lion users and has features and fixes that improve the stability, compatibility, and security of your Mac, including the following: Compatibility improvements when connecting to certain enterprise Wi-Fi networks. Microsoft Exchange compatibility improvements in Calendar. Install Os X Mountain Lion V10.8.5.dmg Download - dlever. OS X Mountain Lion is available now as a download from the Mac App Store. Just click the Mac App Store icon in your dock, purchase Mountain Lion, and follow the onscreen instructions to install it. Mountain Lion will not only make your Mac work better, it also makes your Mac work even. How To Install Os X Mountain Lion 10.8.5.dmg Free Our Suggestion/Verdict About Mac OS X Mountain Lion: You believe or not, Apple has revamped plenty of things with this Mac OS, as some new security concerning options were being added and plethora of other performance based improvements are also existing, which are definitely borrowed from iOS. The Mac Mountain Lion picked up the trust of the end-clients with the expansion of Siri and Apple pay support in safari. To know more about macOS Sierra 10.12 ISO and DMG Image, visit our page for the details. Overview of MacOS X Mountain Lion 10.8 ISO. The Mac OS X Mountain Lion 10.8 ISO varied from its successors with progressive highlights.
For the protection of our customers, Apple does not disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available. To learn more about Apple Product Security, see the Apple Product Security website.
For information about the Apple Product Security PGP Key, see 'How to use the Apple Product Security PGP Key.'
Where possible, CVE IDs are used to reference the vulnerabilities for further information.
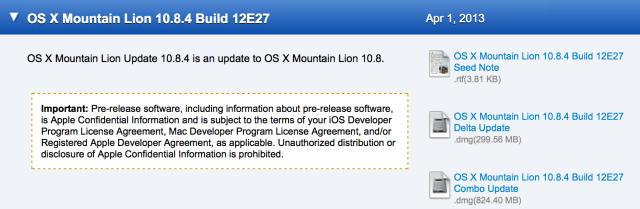
Os X Mountain Lion 10.8.4 Dmg Download
To learn about other Security Updates, see 'Apple Security Updates.'
OS X Mountain Lion v10.8.4 and Security Update 2013-002
Note: OS X Mountain Lion v10.8.4 includes the content of Safari 6.0.5. For further details see About the security content of Safari 6.0.5.

CFNetwork
Available for: OS X Mountain Lion v10.8 to v10.8.3
Impact: An attacker with access to a user's session may be able to log into previously accessed sites, even if Private Browsing was used
Description: Permanent cookies were saved after quitting Safari, even when Private Browsing was enabled. This issue was addressed by improved handling of cookies.
CVE-ID
CVE-2013-0982 : Alexander Traud of www.traud.de

CoreAnimation
Available for: OS X Mountain Lion v10.8 to v10.8.3
Impact: Visiting a maliciously crafted site may lead to an unexpected application termination or arbitrary code execution
Description: An unbounded stack allocation issue existed in the handling of text glyphs. This could be triggered by maliciously crafted URLs in Safari. The issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0983 : David Fifield of Stanford University, Ben Syverson
Os X Mountain Lion 10.8.4 Dmg Download
CoreMedia Playback
Available for: OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution
Description: An uninitialized memory access issue existed in the handling of text tracks. This issue was addressed by additional validation of text tracks.
CVE-ID
CVE-2013-1024 : Richard Kuo and Billy Suguitan of Triemt Corporation
CUPS
Available for: OS X Mountain Lion v10.8 to v10.8.3
Impact: A local user in the lpadmin group may be able to read or write arbitrary files with system privileges
Description: A privilege escalation issue existed in the handling of CUPS configuration via the CUPS web interface. A local user in the lpadmin group may be able to read or write arbitrary files with system privileges. This issue was addressed by moving certain configuration directives to cups-files.conf, which can not be modified from the CUPS web interface.
CVE-ID
CVE-2012-5519
Directory Service
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8
Impact: A remote attacker may execute arbitrary code with system privileges on systems with Directory Service enabled
Description: An issue existed in the directory server's handling of messages from the network. By sending a maliciously crafted message, a remote attacker could cause the directory server to terminate or execute arbitrary code with system privileges. This issue was addressed through improved bounds checking. This issue does not affect OS X Lion or OS X Mountain Lion systems.
CVE-ID
CVE-2013-0984 : Nicolas Economou of Core Security
Disk Management
Available for: OS X Mountain Lion v10.8 to v10.8.3
Impact: A local user may disable FileVault
Description: A local user who is not an administrator may disable FileVault using the command-line. This issue was addressed by adding additional authentication.
CVE-ID
CVE-2013-0985
OpenSSL
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8, OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: An attacker may be able to decrypt data protected by SSL
Description: There were known attacks on the confidentiality of TLS 1.0 when compression was enabled. This issue was addressed by disabling compression in OpenSSL.
CVE-ID
CVE-2012-4929 : Juliano Rizzo and Thai Duong
OpenSSL
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8, OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: Multiple vulnerabilities in OpenSSL
Description: OpenSSL was updated to version 0.9.8x to address multiple vulnerabilities, which may lead to denial of service or disclosure of a private key. Further information is available via the OpenSSL website at http://www.openssl.org/news/
CVE-ID
CVE-2011-1945
CVE-2011-3207
CVE-2011-3210
CVE-2011-4108
CVE-2011-4109
CVE-2011-4576
CVE-2011-4577
CVE-2011-4619
CVE-2012-0050
CVE-2012-2110
CVE-2012-2131
CVE-2012-2333
QuickDraw Manager
Available for: OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.2
Impact: Opening a maliciously crafted PICT image may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of PICT images. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0975 : Tobias Klein working with HP's Zero Day Initiative
QuickTime
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8, OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of 'enof' atoms. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0986 : Tom Gallagher (Microsoft) & Paul Bates (Microsoft) working with HP's Zero Day Initiative
QuickTime
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8, OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: Viewing a maliciously crafted QTIF file may lead to an unexpected application termination or arbitrary code execution
Description: A memory corruption issue existed in the handling of QTIF files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0987 : roob working with iDefense VCP
QuickTime
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8, OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: Viewing a maliciously crafted FPX file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of FPX files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0988 : G. Geshev working with HP's Zero Day Initiative
QuickTime
Available for: OS X Mountain Lion v10.8 to v10.8.3
Impact: Playing a maliciously crafted MP3 file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of MP3 files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2013-0989 : G. Geshev working with HP's Zero Day Initiative
Ruby
Available for: Mac OS X 10.6.8, Mac OS X Server 10.6.8
Impact: Multiple vulnerabilities in Ruby on Rails
Description: Multiple vulnerabilities existed in Ruby on Rails, the most serious of which may lead to arbitrary code execution on systems running Ruby on Rails applications. These issues were addressed by updating Ruby on Rails to version 2.3.18. This issue may affect OS X Lion or OS X Mountain Lion systems that were upgraded from Mac OS X 10.6.8 or earlier. Users can update affected gems on such systems by using the /usr/bin/gem utility.
CVE-ID
CVE-2013-0155
CVE-2013-0276
CVE-2013-0277
CVE-2013-0333
CVE-2013-1854
CVE-2013-1855
CVE-2013-1856
CVE-2013-1857
SMB
Available for: OS X Lion v10.7 to v10.7.5, OS X Lion Server v10.7 to v10.7.5, OS X Mountain Lion v10.8 to v10.8.3
Impact: An authenticated user may be able to write files outside the shared directory
Description: If SMB file sharing is enabled, an authenticated user may be able to write files outside the shared directory. This issue was addressed through improved access control.
CVE-ID
CVE-2013-0990 : Ward van Wanrooij

Note: Starting with OS X v10.8.4, Java Web Start (i.e., JNLP) applications downloaded from the Internet need to be signed with a Developer ID certificate. Gatekeeper will check downloaded Java Web Start applications for a signature and block such applications from launching if they are not properly signed.
You can use the codesign utility to sign the JNLP file, which will attach the code signature to the JNLP file as extended attributes. To preserve these attributes, package the JNLP file in a ZIP, XIP, or DMG file. Be careful using the ZIP format, as some third-party tools might not capture the required extended attributes correctly.
Learn more at Technical Note TN2206: OS X Code Signing In Depth.